Cleanroom Recovery Architecture: How to Design a Secure Isolated Recovery Environment
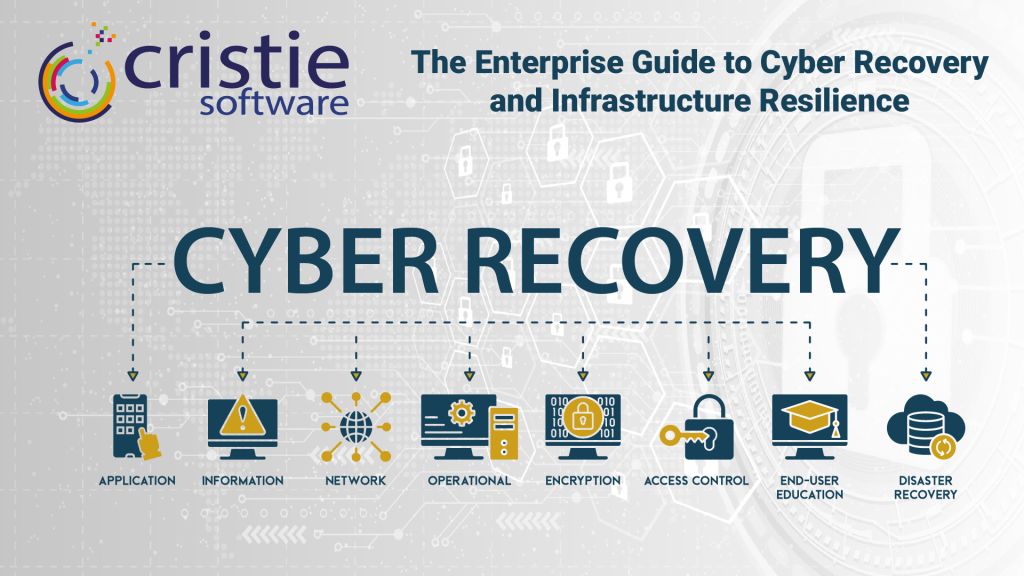
Learn how to build a secure clean room recovery environment to safely restore, verify, and investigate systems after a cyberattack. Discover the essential technologies, isolation strategies, and recovery best practices organizations need to prevent reinfection, validate backups, and strengthen cyber resilience during ransomware and disaster recovery scenarios.